Cloud and container security: How asset management helps you detect configuration and security gaps

Cybersecurity Asset Management Use Case #3
The story of the pandemic has been one of digital transformation. For many organizations, this means a huge growth in the use of cloud computing, containers, and DevOps to support a more productive workforce and create innovative customer experiences. But cloud is complicated. Assets come and go in the blink of an eye, third-party code is commonplace but opaque, and scale can be immense. How do you get the visibility and control you need to understand the size and shape of your cloud attack surface at any given point in time? And then fix it?
The answer lies with continuous cyber asset management and controls monitoring that empower IT and security teams to optimize their cloud security posture—across any heterogenous environment.
The story so far
While digital transformation has taken a huge leap forward during the pandemic, it’s a story that began long before COVID-19 hit and will endure long after it has receded from view. The worldwide public cloud services market is forecast to grow by 18% this year to reach $305 billion, and will surged by a similar rate next year to top $362 billion, according to Gartner. That includes SaaS apps used to drive user productivity, and IaaS and PaaS to build software in-house.
The challenge with the cloud, is that while it offers the prospect of making it easier to do things quickly, it also makes it easier to do stuff badly—and at scale. Part of the problem lies with the open-source templates and repositories increasingly popular among DevOps teams to accelerate time-to-value. These dependencies may have dependencies of their own, creating a complex web of potential vulnerabilities and misconfigurations to unravel and manage. Recent research reveals that 63% of third-party code templates used to build cloud infrastructure have insecure configurations, while 96% of third-party container applications deployed in cloud infrastructure contain known vulnerabilities.
More concerning still is that threat actors are now actively targeting this yawning gap in cloud security. Separate research points to a 650% year-on-year increase in upstream attacks on the software supply chain, where bad actors are injecting new bugs into open-source projects. Another report claims attackers can detect cloud misconfigurations in as little as 10 minutes, but that just 10% of organizations are remediating within that same time frame.
Other visibility and security challenges in the cloud include:
- A fast-growing and changing attack surface, as democratization empowers different business teams to create accounts and spin up new assets for projects. These VMs and containers can disappear just as quickly, making continuous monitoring essential.
- Mounting complexity, as organizations build out hybrid clouds from multiple vendors. A 2021 report claims that 92% of enterprises now have a multi-cloud strategy while 80% have a hybrid cloud strategy. More platforms mean more management consoles and security tooling, different terminology, siloed visibility, and challenges creating and enforcing security policy.
The visibility and automation you need
The combined impact of these challenges is to leave organizations flying blind in the cloud—unsure when new vulnerabilities and misconfigurations are exposing them to serious risk. It could be a newly deployed container containing code vulnerabilities. Or an unencrypted storage volume. Whatever the risk, you need continuous visibility and control.
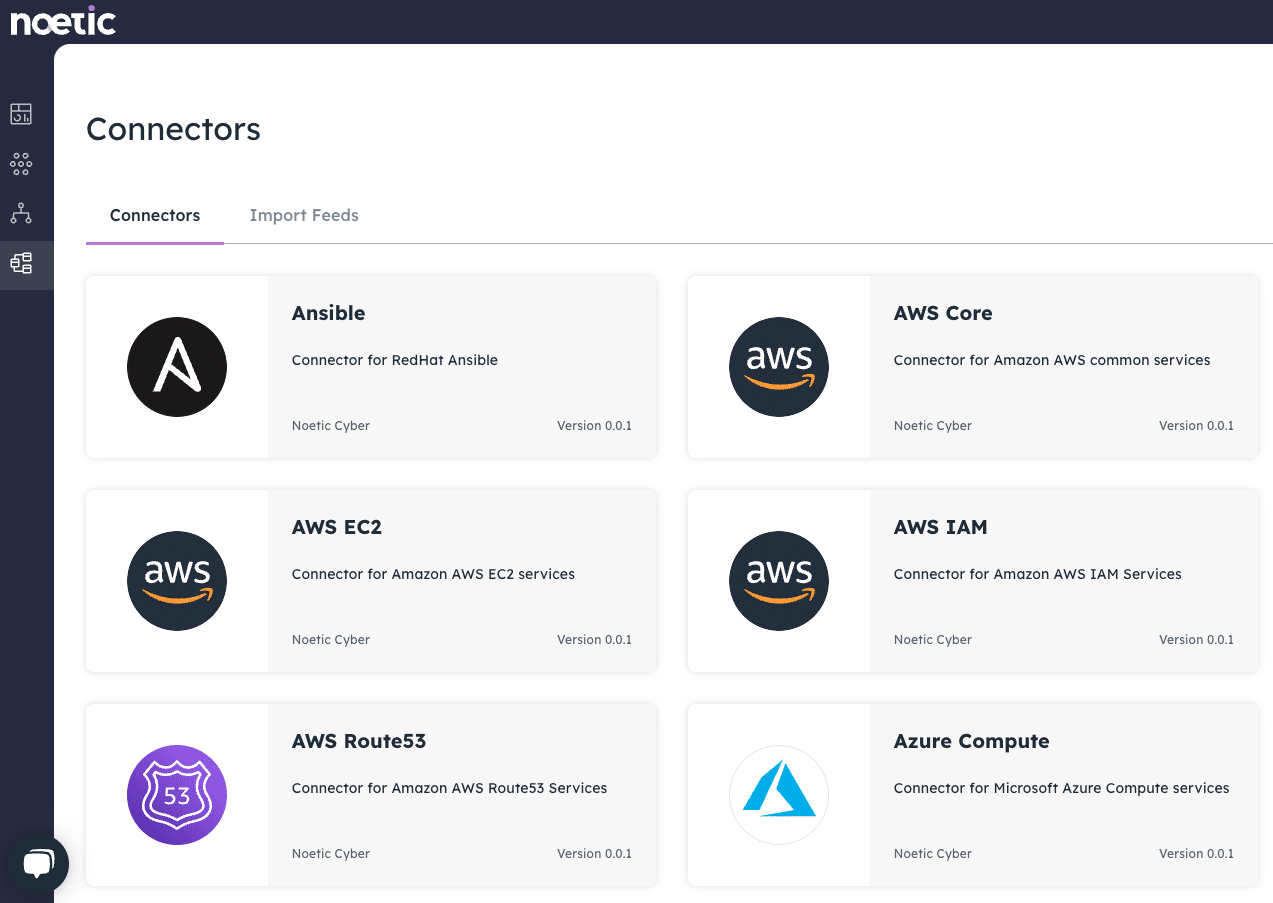
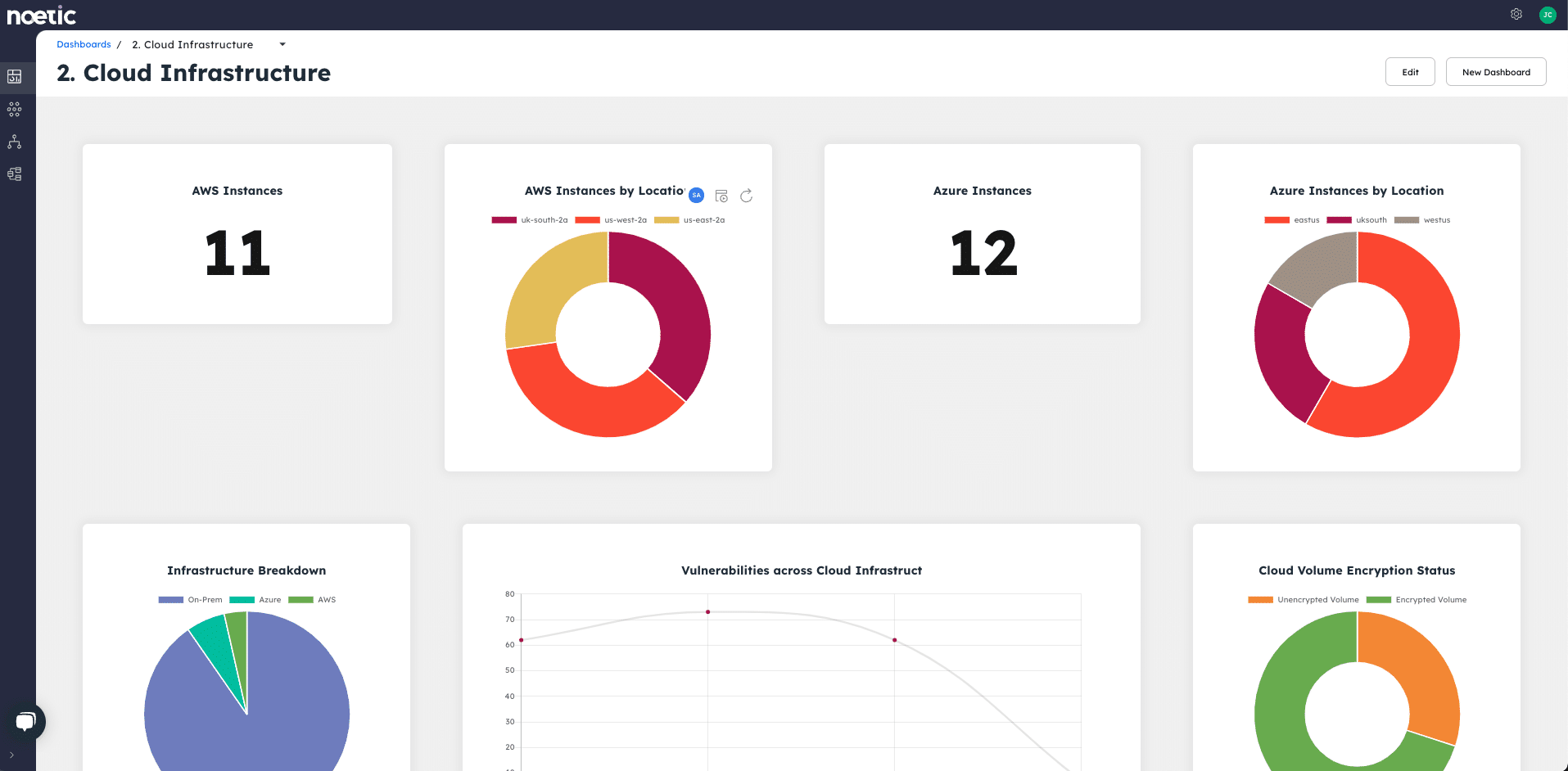
Noetic provides that visibility by leveraging data from AWS, Google, Azure, Kubernetes, VMware, and other major cloud players. This provides an exact and up-to-date baseline of the entire cloud “as built” estate, no matter how many providers or platforms you’re running workloads across. This data is combined with other security and IT management tooling and aggregated and correlated to provide a full picture of all assets running in the cloud estate, and typically it would also include on-premises deployments as well. Security teams can now understand where all their assets are, what their current security posture is, and how that relates to our security policies and business dependencies.
It’s good to understand whether several of your cloud systems are not currently part of your vulnerability scanning process for example, but it becomes critical information if those services are supporting a share price affecting application. This level of business context is vital to making good security decisions.
Visibility is only the first step though. Automation is commonly used for a wide range of cloud use cases, and security is no exception. We can apply our powerful workflow engine to help you automatically enforce your security policy—returning your cloud assets to their “ideal” security posture and continuously correcting compliance drift. This is what we refer to as a Noetic ‘loop’ where the platform is constantly reviewing the current state of assets against the desired level and working to adjust as appropriate. A Noetic loop should be both comprehensive and continuous, querying newly identified and updated assets and adding them into the existing process.
For cloud-based assets, this might include encrypting attached storage volumes, enforcing multi-factor authentication, or reconfiguring access control to open S3 buckets. Because the Noetic platform is constantly looking for new assets, and new relationships between existing assets, we know what’s going on, and where risk is most acute, always.
The bottom line for Noetic customers is:
- Reduced risk of reputational and financial damage, by identifying coverage gaps, eliminating misconfigurations and vulnerabilities.
- Identify critical assets and allow teams to prioritize workloads making security teams more efficient, and freed-up to work on other tasks thanks to a high degree of automation.
- Greater confidence to drive digital transformation for competitive advantage.
That’s the kind of competitive advantage organizations need as they look to extract maximum value from their cloud investments. This solution brief provides more information on the Noetic solution, or you can register for a more detailed platform walkthrough demo.
Our next use case blog will look at how the Noetic solution co-exists, and provides value to existing IT Asset Management (ITAM), Software Asset Management (SAM) and CMDB deployments.
