Exploring the Evolution: NIST Cybersecurity Framework 2.0
Navigating the ever-shifting terrain of cybersecurity demands a resilient framework capable of adapting to the relentless evolution of digital threats. In this fast-paced landscape, the National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF) has become a stalwart guide, providing organizations with a roadmap to fortify their defenses and mitigate cyber risks.
In this comprehensive exploration, we delve deep into the history, evolution, and impact of the NIST Cybersecurity Framework. From its inception to the unveiling of NIST CSF 2.0, we examine the framework’s journey, the rationale behind its updates, and the anticipated benefits and challenges organizations may encounter in its adoption.
The History of the NIST Cybersecurity Framework (CSF)
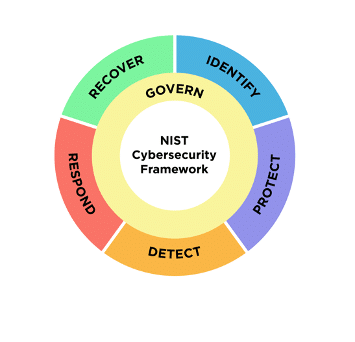
Since its inception in 2014 and subsequent update to version 1.1 in 2018, the NIST CSF has become a cornerstone for global security teams, providing a roadmap to mitigate cyber risks and bolster cybersecurity initiatives. Originally tailored for federal agencies, its influence has transcended sectors, finding adoption across diverse industries due to its intuitive structure centered around five core functions: Identify, Protect, Detect, Respond, and Recover.
In the five years since its last major revision, the tech landscape has undergone significant transformations, marked by the rapid expansion of cloud computing, the paradigm shifts towards hybrid work models, and the recognition of the supply chain as a pivotal attack vector. Recognizing the need to adapt to these evolving challenges, NIST commenced a consultation process in February 2022, inviting input from over 130 organizations, including industry giants like Microsoft, American Airlines, and a coalition of prominent security vendors and practitioners.
Following an exhaustive review of community feedback, NIST unveiled the draft iteration of CSF 2.0 on August 8, 2023, marking the beginning of a feedback phase that extended until November 2023. Finally, after thorough consideration of the feedback received, the agency officially released NIST CSF 2.0 on February 26, 2024.
What’s new in NIST CSF 2.0?
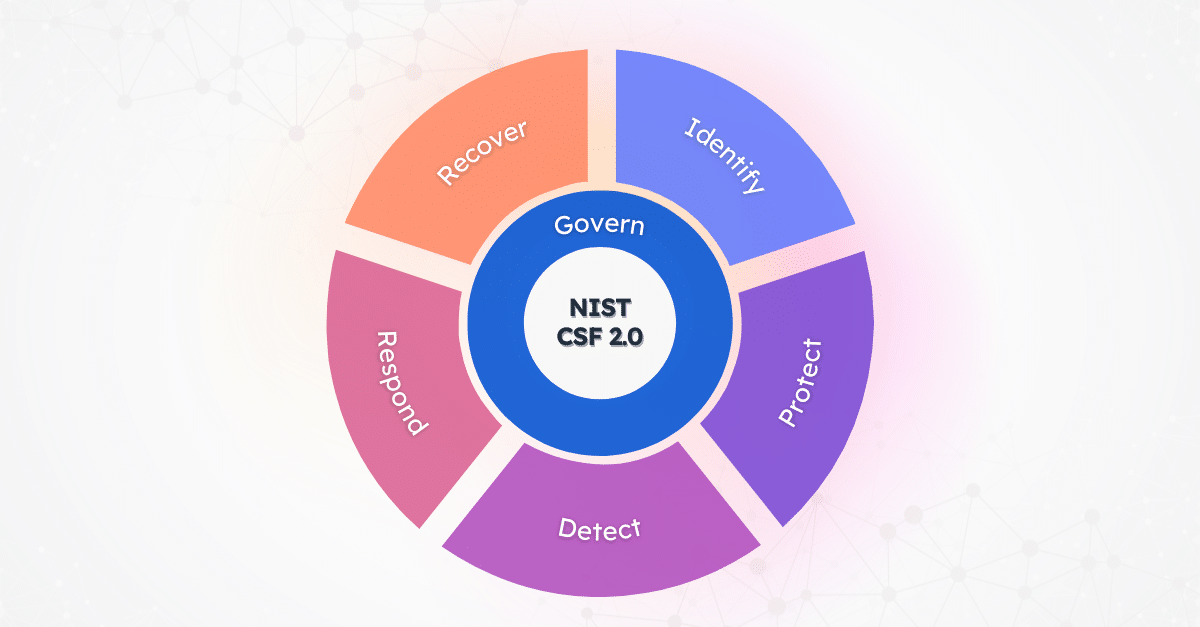
Building upon the foundation laid by its predecessors, CSF 2.0 represents a significant evolution, catering to organizations of all sizes and sectors, transcending its original focus on federal agencies. With enhancements such as the introduction of the pivotal sixth function – Govern – and improved implementation guidance, CSF 2.0 equips organizations with the tools needed to navigate the complexities of the modern cybersecurity landscape.
NIST Introduces the “Govern” Function
In the evolution of cybersecurity frameworks, NIST has taken a significant step forward with the release of Cybersecurity Framework 2.0 (CSF 2.0). While its predecessor, CSF 1.1, focused on five fundamental components of a robust cybersecurity program, the latest iteration introduces a pivotal sixth function: Govern.
The “Govern” function in CSF 2.0 emphasizes cybersecurity as a major enterprise risk, highlighting its importance alongside other critical considerations such as finance and reputation. This function encourages senior leadership involvement in cybersecurity strategy by emphasizing informed decision-making processes and organizational ownership of cybersecurity objectives.
Elements under the new Govern function include defining risk management objectives, organizational ownership, legal and regulatory requirements. It also covers external stakeholders to reflect the growing importance of maintaining cyber governance across the extended supply chain.
Enhanced Implementation Guidance
Recognizing the importance of practical implementation advice, CSF 2.0 offers improved and expanded guidance to assist organizations in effectively implementing the framework. This enhanced guidance aims to bridge the gap between theory and practice, enabling organizations to translate the principles of the framework into actionable cybersecurity measures.
CSF 2.0 provides comprehensive instructions on creating profiles tailored to an organization’s unique risk landscape, facilitating the practical application of the framework. CSF was originally designed for government agencies and critical national infrastructure; these changes are intended to make it more consumable to a wider range of industry sectors and less complex, smaller businesses that are increasingly a target for ransomware gangs.
Additionally, by promoting senior leadership involvement and providing practical tools for implementation, the framework strengthens organizational resilience against cyber threats. The updated framework also aligns more closely with industry standards and best practices, facilitating interoperability and alignment with existing cybersecurity initiatives. This alignment enhances collaboration and information sharing across sectors, fostering a more cohesive approach to cybersecurity risk management.
The Impact of NIST CSF 2.0
Adopting NIST CSF 2.0 enables organizations to establish a stronger foundation for their cybersecurity strategies. The framework’s expanded scope, including the addition of the “Govern” function and improved implementation guidance, empowers organizations to effectively manage cybersecurity risks across various sectors and sizes.
While the improved implementation guidance aims to bridge the gap between theory and practice, organizations may still encounter challenges in effectively implementing the framework, including:
- Resource Allocation: Adopting CSF 2.0 may require organizations to allocate additional resources, both in terms of time and finances, to effectively implement the framework. This could pose a challenge, particularly for smaller organizations with limited cybersecurity budgets.
- Organizational Complexity: The expanded scope and improved implementation guidance of this latest version may introduce complexity for organizations, especially those with decentralized structures or diverse operational environments. Managing this complexity and ensuring alignment across various departments or business units could present challenges.
- Skill and Knowledge Gaps: Implementation may require organizations to enhance their cybersecurity expertise and capabilities. Addressing skill and knowledge gaps among staff members to effectively utilize the framework could be a significant challenge, particularly for organizations with limited cybersecurity expertise or experience.
Overall, while NIST CSF 2.0 offers significant benefits in terms of flexibility, resilience, and streamlined implementation, organizations may also face challenges related to resource constraints, complexity management, and knowledge gaps. Addressing these challenges proactively can help organizations maximize the value of CSF 2.0 and strengthen their cybersecurity posture effectively.
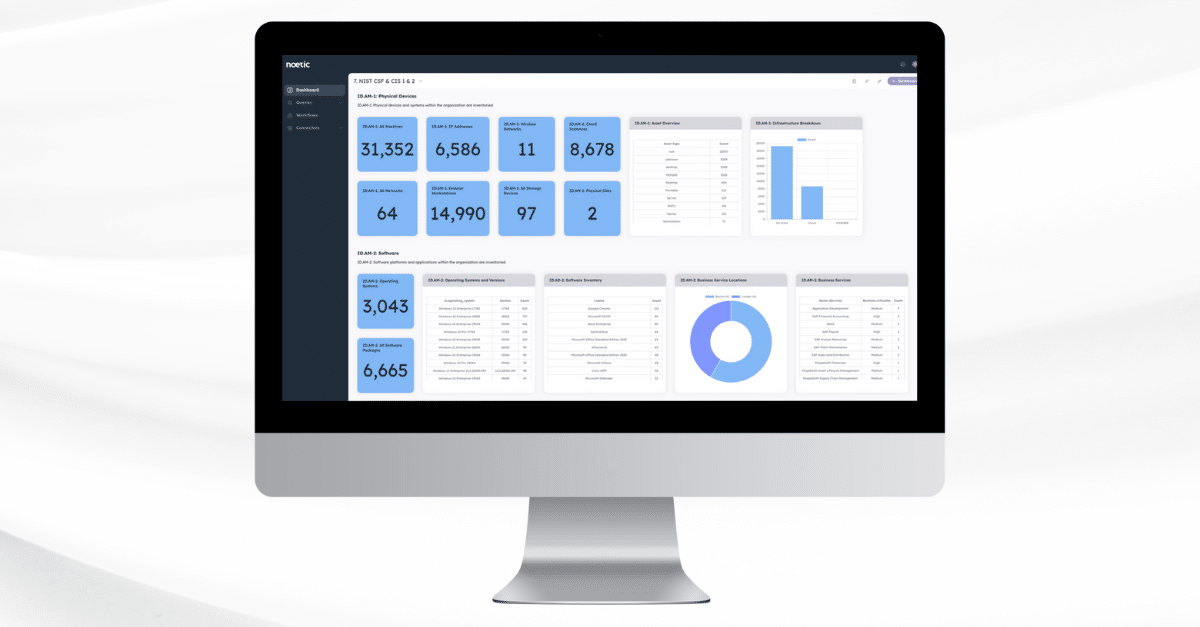
Ready to fortify your organization’s cybersecurity strategy with the power of NIST CSF 2.0? Join an upcoming live demonstration to see how Noetic can help.

