Mastering the Art of Vulnerability Prioritization: A Step-by-Step Guide
The average vulnerability and patch management backlog now contains over 100,000 vulnerabilities, making a process for better vulnerability prioritization essential to ensure the most critical threats are addressed. In this blog, we’ll delve deeper into the different dimensions of prioritizing vulnerabilities—severity, exploitability, exposure, business context, and compensating controls—as well as explore the best practices, tools, and resources that empower organizations to fortify their security posture and stay ahead of potential threats.
Understanding Vulnerability Prioritization
Vulnerability prioritization is the process of systematically evaluating and ranking vulnerabilities based on their potential impact and exploitability to help organizations identify which should be addressed first. This is the third–and arguably most important–step in the continuous threat exposure management (CTEM) process. By better prioritizing vulnerabilities, organizations can effectively allocate their resources and focus on mitigating the most critical risks to their systems and data.
To understand vulnerability prioritization, it is crucial to recognize that not all vulnerabilities are created equal. Some vulnerabilities may have a higher potential impact, while others may be more easily exploitable. The key is to assess and rank vulnerabilities based on these factors to identify the most critical ones.
The Four Elements of Effective Vulnerability Prioritization
Effective prioritization helps security teams to use their limited resources judiciously, focusing on the most critical vulnerabilities to their business that could lead to severe breaches or system compromises. It not only enhances the efficiency of remediation efforts, but also fortifies an organization’s overall security posture by ensuring that the most pressing threats are addressed promptly.
The ability to discern which vulnerabilities require immediate attention is paramount. To do so effectively, organizations must structure their approach around the four critical dimensions of effective prioritization: severity, exploitability, business context, and controls.
- Severity: Magnitude of the Threat
Severity refers to the potential impact a vulnerability can have on a system, application, or organization. Vulnerabilities are typically rated based on a scale such as the Common Vulnerability Scoring System (CVSS), which recently had a major upgrade to v4.0. CVSS considers factors like access complexity, authentication requirements, and impact on confidentiality, integrity, and availability.
To evaluate a vulnerability’s overall severity:
- Establish a Clear Scoring System: Develop a well-defined scoring system that aligns with industry standards like CVSS. This provides a consistent and objective way to assess severity.
- Regularly Update Severity Ratings: Periodically reevaluate the severity of vulnerabilities as new information emerges, or threat landscapes evolve.
- Allocate Resources Proportionally: Allocate more resources to addressing high-severity vulnerabilities while balancing overall risk management efforts.
A concerning recent development for security teams has been the delay in updating critical information in the NIST National Vulnerability Database (NVD). This means that many of the latest CVEs published lack the necessary context to prioritize effectively. There are various industry efforts underway to address this which Noetic is tracking.
- Exploitability: Likelihood of Exploitation
Exploitability is the ease in which a vulnerability can be exploited by a malicious actor. Key aspects that define exploitability include ease of exploitation and public exploitability.
To effectively assess the exploitability:
- Leverage Vulnerability Intelligence: Stay informed about the latest threats, exploits, and attack patterns to understand the current exploit landscape. Several resources exist and are widely used to help organizations understand the urgency of vulnerabilities, including:
- The Cybersecurity Infrastructure Security Agency (CISA) maintains a Known Exploited Vulnerabilities (KEV) catalog. The CISA KEV catalog is a list of known vulnerabilities that malicious actors actively use to compromise systems.
- The Exploit Prediction Scoring System (EPSS) leverages estimates the probability of a software vulnerability being exploited according to a data-driven algorithm developed by the Forum of Incident Response and Security Teams (FIRST)
- Assess Patch Availability: Prioritize vulnerabilities for which patches or mitigations are not available or are difficult to implement.
- Consider Vulnerability Exposure: Evaluate if a vulnerability is exposed to the internet or within the organization’s internal network, impacting the potential for exploitation. Understanding the potential attack path of the adversary is important here.
Even one additional layer of intelligence can significantly improve the vulnerability prioritization process. However, even critical, actively exploited vulnerabilities is not foolproof—and can still leave an overwhelming backlog.
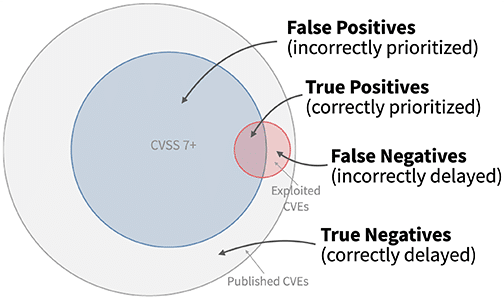
Image Source: FIRST.org
- Business Context: Environmental Considerations
Context is about understanding how a vulnerability relates to the specific organizational environment, including the system’s role, data it handles, and its criticality to business operations. The vulnerability on a mission-critical system will have a higher priority than one in a non-production environment.
To understand business context, organizations need to understand what they have, and how it is connected. An essential building block of a vulnerability prioritization program is a continuously-updated cyber asset inventory.
In 2022, CISA issued directive BOD 23-01 which requires federal agencies to maintain an up-to-date asset inventory and to scan for new assets at least every 7 days, this should be the minimum required of organizations today.
By mapping the technical posture of all assets–machines, networks, users, datasets, containers, etc.–together with business information of application severity and business location, security teams get visibility into this context.
- Define Organizational Risk Tolerance: Understand the organization’s risk tolerance and align vulnerability prioritization accordingly.
- Account for Asset Sensitivity: Consider the sensitivity of the assets affected by the vulnerability and their importance to the organization’s operations.
- Flag Business-Critical Systems: Focus on vulnerabilities that could have a direct impact on business continuity, financial operations, or sensitive data.
- Controls: Existing Safeguards & Countermeasures
Controls refer to the security measures and safeguards in place to mitigate the potential impact of a vulnerability. Evaluating vulnerabilities in the context of available controls helps in efficient resource allocation.
Best practices to incorporate the controls dimension include:
- Review Current Security Measures: Assess the effectiveness of compensating security controls, such as firewalls, intrusion detection systems, and access controls.
- Consider Defense-in-Depth Strategies: Give higher priority to vulnerabilities in systems lacking multiple layers of defense.
- Account for Security Hygiene: Prioritize vulnerabilities in systems with poor security practices or outdated security configurations.
| Definition | Why it’s important | Key Considerations |
|---|---|---|
| Severity is the impact a vulnerability can have on a system, application, or organization | Ensures that resources are allocated to address the most damaging and likely vulnerabilities first. | Potential Damage: Consider the potential harm the vulnerability could cause in terms of data loss, financial impact, or operational disruption. Data Exposure: Evaluate the type of data that could be exposed if the vulnerability is exploited, such as sensitive customer information or financial records. Ease of Exploitation: Assess the level of skill and effort an attacker would need to exploit the vulnerability successfully. |
| Exploitability focuses on the likelihood that a vulnerability will be exploited by malicious actors. | Helps teams to focus on vulnerabilities that are most likely to be targeted by attackers. | Availability of Exploits: Check if there are known and accessible exploits targeting the vulnerability, as this increases the likelihood of exploitation. Ease of Exploitation: Evaluate how easy it is for a potential attacker to exploit the vulnerability. Vulnerabilities that are easy to exploit are often prioritized higher. Exposure to the Internet: Consider if the affected system is exposed to the internet, as this increases the risk of exploitation. |
| Context is the understanding of the unique circumstances and environment of an organization | Empowers teams to tailor the response to vulnerabilities based on their potential impact on the organization. | Asset Criticality: Vulnerabilities on critical assets, such as servers containing sensitive data, should take precedence over those on less critical assets. Business Impact: Assess how a vulnerability might impact the organization’s core business functions, reputation, or regulatory compliance. Sensitive Data Handling: Evaluate if the affected systems handle sensitive data and the potential impact on privacy and compliance. |
| Controls are the existing security measures or defenses in place that can mitigate the impact of a vulnerability. | Ensures that investments are made where they can provide the most significant security improvements. | Mitigation Controls: If strong mitigation controls are already in place for a vulnerability, it may be lower on the priority list since the risk is effectively reduced. Compensating Controls: Assess whether compensating controls can be implemented to reduce the risk of a vulnerability while a patch or remediation plan is developed. Resilience of the System: Consider the system’s overall resilience to potential exploitation and its ability to limit the damage. |
Prioritizing vulnerabilities is a multifaceted process that requires a thorough evaluation of severity, exploitability, context, and compensating controls. By adopting a systematic approach that integrates these dimensions, organizations can effectively allocate resources, reduce risks, and enhance their overall cybersecurity posture. Staying vigilant and continually refining this approach is crucial in the dynamic landscape of cybersecurity.
When done correctly, effective vulnerability prioritization provides a roadmap for organizations to navigate the complex landscape of threat and vulnerability management, enabling them to allocate resources wisely, align cybersecurity efforts with business goals, and ultimately build a resilient security posture that can effectively combat evolving cyber threats.
Noetic empowers teams to prioritize critical threats and vulnerabilities based on a comprehensive array of insights, including technical asset data gathered from vulnerability scanners and ITAM tools, as well as considerations of intra-asset relationships and interconnectivity. We integrate third-party vulnerability intelligence from esteemed sources like MITRE, FIRST, NIST, and CISA, focusing on severity and exploitability. Additionally, the platform factors in relevant business context such as affected users, sensitive data, and critical applications, alongside assessments of compensating security controls that are in place.
Discover more about how Noetic assists team in effectively prioritizing critical threats and exposures: How to Implement CTEM with Noetic.
Frequently Asked Questions (FAQs)
- How do organizations typically measure the success or effectiveness of their vulnerability prioritization strategies over time?
Organizations often measure the success of their vulnerability prioritization strategies by tracking key performance indicators (KPIs) such as the reduction in the number of high-severity vulnerabilities over time, the decrease in the average time to remediate critical vulnerabilities, or the overall improvement in their security posture as demonstrated through penetration testing or third-party security assessments.
Additionally, they may assess the cost-effectiveness of their remediation efforts by comparing the investment in security measures to the potential losses from successful cyberattacks. Regular reviews and audits of the vulnerability management process can also provide insights into its efficacy, allowing organizations to refine their strategies based on lessons learned and evolving threat landscapes.
- Are there any emerging trends or technologies in vulnerability prioritization organizations should be aware of?
One emerging trend in vulnerability prioritization is the integration of machine learning and artificial intelligence (AI) algorithms to analyze vast amounts of security data and identify patterns indicative of high-risk vulnerabilities. These advanced analytical techniques can help organizations detect previously unseen threats, predict future attack vectors, and automate decision-making processes to prioritize vulnerabilities more efficiently. Furthermore, the adoption of threat intelligence platforms that leverage AI-driven risk scoring models and predictive analytics enables organizations to stay ahead of emerging threats by continuously monitoring and analyzing cybersecurity trends and attack patterns.
- Can you provide examples of real-world scenarios where effective vulnerability prioritization has significantly mitigated cybersecurity risks for organizations?
Effective vulnerability prioritization has proven instrumental in mitigating cybersecurity risks for organizations across various industries. For instance, a financial institution might prioritize vulnerabilities on critical infrastructure components such as payment processing systems to prevent potential disruptions to customer transactions or data breaches.
Similarly, a healthcare organization may focus on patching vulnerabilities in electronic health record (EHR) systems to safeguard sensitive patient information and maintain compliance with data protection regulations. By prioritizing vulnerabilities based on their potential impact on business operations, reputation, and regulatory compliance, these organizations can allocate resources more effectively and proactively address the most critical security threats before they are exploited by malicious actors.
